All You Need to Know About Crypto Wallets
Cryptocurrencies have drawn a lot of interest since the launch of Bitcoin in 2009, and many countries now acknowledge cryptocurrency trading as a legal sector. However, regulatory approaches vary: some countries are still developing clear frameworks, while others, like China and Egypt, have imposed bans.
Despite this, the interest in cryptocurrencies continues to grow, with more individuals and businesses exploring how to trade them effectively.
A cryptocurrency wallet is one of the most crucial tools for handling digital assets. It allows users to store various types of cryptocurrencies, track balances, and conduct transactions. This article will cover the basics of crypto wallets, how they function, and why cryptocurrency regulation is crucial today.
What Is a Crypto Wallet?
A crypto wallet contains data about digital currencies, much like a conventional wallet does with cash. It manages cryptographic keys required for asset operations or authenticates users to access platform services. Additionally, it collects data related to user addresses, including asset balances, transaction history, and more.
Crypto wallets simplify blockchain data by displaying only the information relevant to the user’s addresses. Private keys are vital in this process, as they must be securely stored. Public keys and addresses are derived from private keys, and only the owner can sign transactions using these addresses before they are added to the blockchain.
The recipient of funds follows a similar process, using their private keys to manage assets. These operations collectively form a blockchain. While many cryptocurrencies have unique blockchains, numerous crypto assets utilize existing blockchains from other currencies.

Crypto Wallet Types and Categories
Crypto wallets come in diverse types and categories. They differ by accessibility, level of security, how users store their keys, and even the type of cryptocurrency they accept.
Paper wallets, mobile wallets, and hardware wallets are among the different types of crypto wallets. Each kind meets a range of user needs by providing varying degrees of ease and security. When users choose crypto wallets here are the main types they can consider.
Multi-Currency Cryptocurrency Wallets
Multi-currency cryptocurrency wallets are specialized applications or devices designed to store, send, and receive different cryptocurrencies within a single platform. Their main purpose is to simplify the management of digital assets by eliminating the need for multiple separate wallets for each cryptocurrency.
In the blockchain world, each cryptocurrency operates on its own technology, and without multi-currency wallets, users would have to install separate crypto apps to manage each type of token. This is not only inconvenient but also increases the risks of losing data or funds due to having to memorize multiple passwords and seed phrases.

Decentralized Finance Wallets
Decentralized finance wallets are specialized tools that allow users to interact with DeFi platforms without intermediaries. They provide access to features such as staking, lending, liquidity farming, and trading on decentralized exchanges (DEX).
DeFi wallets work directly with blockchains and connect to decentralized applications (dApps) via Web3 technology, allowing assets to be managed directly in a browser or mobile wallet program.
However, security depends on the user: they sign transactions themselves and control their funds, but there is a risk of asset loss when interacting with unreliable platforms.
The main features of DeFi wallets include staking, which comes in two types: traditional staking (freezing tokens to support a network such as Ethereum 2.0) and DeFi staking (placing assets in smart contracts to generate revenue).
Users can borrow against collateral or lend their assets via DeFi protocols (such as Aave and Compound). Liquidity farming allows earning by lending tokens to pools of decentralized exchanges such as Uniswap or PancakeSwap, but it comes with risks, including impermanent losses.
Additional features of DeFi wallets include token exchange via built-in DEX services and NFT support. However, not all wallets allow NFT trading – specialized platforms such as OpenSea or Magic Eden are more often used for this purpose.
Thus, DeFi wallets are a universal tool for managing digital assets, but for their safe use, it is important to understand the mechanisms of DeFi products and carefully choose platforms for interaction.
NFT Wallets
NFT wallets are specialized tools that enable users to manage their non-mutualizable tokens. They provide secure private key storage and interaction with the blockchain. NFTs are distinct digital assets with varying values, like artwork, collectibles, or in-game materials.
NFTs require wallets that support tokenization standards, such as ERC-721 and ERC-1155 on the Ethereum blockchain, BEP-721 and BEP-1155 on the Binance Smart Chain, Metaplex on Solana, or Flow NFT Standard on the Flow blockchain. These standards define how NFTs are created, transmitted, and stored on the network.
NFT wallets do not store the tokens themselves but only manage access to them via private keys. In non-custodial wallets, such as MetaMask or Trust Wallet, the user has total control over their keys, making them more secure.
Custodial solutions, such as wallets on centralized exchanges, store keys on the provider side, which is less secure. With NFT wallets, you can connect to marketplaces such as OpenSea, Rarible, Magic Eden, or LooksRare via Web3 integration. This allows you to view, transfer, or sell your NFTs.
Custodial and Non-custodial Wallets
This feature defines how a user wants to store their keys. The wallets where users entrust their keys to third parties or custodians are known as “custodial wallets”. Custodians are responsible for storing cryptographic keys and funds and provide an interface for users to handle crypto.
This kind of wallet is typically web-based, so users can access their wallets via a phone or a web browser by signing into their accounts. In case a user forgets their password, all they need to do is just remember a recovery phrase or follow another simple recovery procedure provided by the custodial service.
Non-custodial crypto wallets work quite differently – users take full responsibility for their public and private keys to remain secure. Losing a wallet or forgetting a password means losing digital coins. At the same time, users don’t have to refer to third parties for managing their keys, instead, they use special software that generates public and private keys for them. Therefore, these wallets are considered more secure than the custodial ones.
Generally, those who only start using crypto wallets prefer a custodial kind of wallet. Users don’t have to bother with storing their private keys, can quickly access their wallets, and perform transactions more seamlessly. Meanwhile, non-custodial wallets could be more secure as the owners of crypto assets manage their keys themselves.
Hot Wallets
Although hot wallets are more convenient for frequent transactions since they are always online, they are not as safe as cold wallets. They are ideal for everyday use, such as trading on crypto exchanges or paying for goods and services.
Examples of hot wallets include mobile cryptocurrency wallet app such as Trust Wallet and MetaMask, as well as web wallets such as Coinbase and Binance. Hot wallets’ primary benefits are their ease of use and rapid access to funds. However, because private keys are kept online, they are susceptible to hacker attacks.
Cold Wallets
Cold wallets are safer for keeping cryptocurrency because they are not online. They are used for long-term storage and are ideal for those who want to protect large sums from cyberattacks. Paper wallets, where private keys are printed on paper and kept in a safe place, and wallets like Ledger and Trezor are examples of cold wallets.
The main advantage of cold wallets is that they maximize protection against hacking, as they are not dependent on the internet. However, because transactions need importing keys into a digital wallet or connecting to a device, they are less practical for frequent transactions.
Mobile/Desktop, Web-Based, or Hardware Wallets
Mobile/desktop, web-based, or hardware crypto wallets determine software applications and devices users utilize to access them.
Web-based wallets can be accessed from a mobile phone or a computer via a web browser. They don’t require installing any cryptocurrency application. Most web-based wallets are custodial, though recently there have been non-custodial options.
Mobile/ desktop wallets require downloading and installing software apps on a computer or smartphone. This software must be compatible with the devices’ operating systems. Therefore, there is a wide range of wallets available for Linux, Windows, Mac, iOS, and Android. This type of wallet is better secured than their web-based analogs and most often is non-custodial.
Hardware wallets are special devices used for storing keys offline. When users sign transactions in hardware crypto wallets, they don’t have to send their keys anywhere and the process of signing happens on the device within a limited time frame, making it more resistant to hacker attempts.
Cryptocurrency Regulation: Why Is It So Important?
While some users are readily investigating the world of Bitcoin, Ethereum, and Tether, others are concerned about the high risks involved and poor law regulations. For this reason, some countries have started working on legal frameworks that could adapt crypto markets to their economic system. The US, most European countries, India, and Australia are among them.
For example, the US government has already taken important steps toward crypto legislation. A cryptocurrency exchange in the US is legal and regulated by the Bank Secrecy Act (BSA). However, the legal framework isn’t consistent yet, and every year more laws appear to regulate digital currency trading.
Among the recent ones was proposed by FinCEN. This regulation requires collecting data on cryptocurrency exchanges and wallets and is expected to be enforced by fall 2022.
Why are regulations in crypto trading necessary and how can this benefit the world of digital currency exchange? Here are the main reasons.
Increased Investor Protection
Despite the fact that blockchain technologies have proved to be of high security, there are frequent attempts of attacks on crypto wallet software. This mainly happens due to users’ poor understanding of how crypto wallets work, e.g. hackers can lure their private keys out and steal coins from wallets or implement other security threats. Apart from that, there may emerge some hidden risks such as a crypto platform going bankrupt or being hacked.
Prevention of Money Laundering and Tax Evasion
As blockchain provides some level of anonymity to its users, it attracts illegal payments that turn regular coins into “dirty” ones. If crypto platforms verify the identities of the trade participants through know-your-customer (KYC) and know-your-business (KYB) procedures, control their source of funds and monitor their transactions, deals, and operations, it’s much easier for governments to prevent illegal money transfers through such platforms, or attempts of tax evasion in their countries.
Increasing Impact on the Global Economy
Blockchain technology and currency trading are constantly developing. There are new types of payments and currencies, and the number of users is continuously growing. All this has more influence on the global economy.
For example, there emerged a new type of currency – stablecoins. These coins are pegged to other assets, usually of well-known reputation and value, such as fiat money like US dollars or other valuables like gold. Recently stablecoins have started to have a deeper effect on economies, e.g. FitchFatings warns that stablecoins can increase risks in a short-term credit market.
Phishing
One of the most often occurring and sneaky threats that users of Bitcoin wallets encounter is phishing. Imagine visiting a website that looks like your preferred wallet or exchange, only to find it to be a scam. Attackers produce virtually perfect replicas of the real thing on false pages, and when you enter your data—passwords, seed phrases, private keys—they wind up in the hands of the frauds.
Always check the website address, use only certified apps, and remember to turn on two-factor authentication to help you stay undercover. These simple measures can save your life savings.
Malware
Malware is similar to cybercriminals who can get onto your computer and take your seed phrases or private keys. One mistake – download a suspicious file or install an untrusted app – and your funds could be at risk. To protect yourself, use quality antivirus software, update your operating system regularly, and be careful about what you download from the internet. Remember, your security is in your hands, and it never hurts to be extra cautious.
Cryptocurrency Wallet Security
Cryptocurrencies are a vital tool for protecting and managing digital assets, but their level of security is directly influenced by user behavior and security protocols. Because cryptocurrencies are decentralized and cannot be restored in the event of loss or theft, wallet security is crucial. Let’s look at basic security methods and the importance of backup and recovery.
Security Methods
- Two-Factor Authentication (2FA): One of the most popular techniques for enhancing security is this one. The user must provide a second factor of identity, such as a physical key, an authenticator app (like Authy or Google Authenticator), or a code from an SMS, in order to access the wallet or complete transactions. Even if attackers know the password, they will have a considerably more difficult time accessing the wallet.
- Multi-signature: With multi-signature technology, a transaction must be verified by several parties. For instance, two or more devices or users may need to sign a transfer. This is particularly useful for corporate wallets or collaborative asset management since it reduces the likelihood of money theft even if one of the keys is stolen.
- Data encryption: Many wallets use encryption to protect private keys and seed phrases. This implies that even if an attacker gains access to the device, they will be unable to decode the data unless they know the password or PIN.
- Hardware wallets: Wallets such as Ledger or Trezor store private keys offline, making them virtually invulnerable to hacking attacks over the internet. They are considered one of the safest ways to store cryptocurrencies.
Backup and Restore
- Seed-phrase: You can use a seed phrase, sometimes called a mnemonic phrase, which is a collection of 12 or 24 syllables, to retrieve your wallet in the event that your device is lost or your data is corrupted. It is essential to write this phrase down and save it in a secure location instead of on digital storage to lessen the likelihood of hacking.
- Backup: Some wallets enable you to backup your data, which can be kept on hardware crypto wallets or external media like USB drives. In the event that you misplace your primary device, this offers an additional degree of security.
- Test transactions: To ensure your wallet is functioning correctly, it is preferable to do a test transaction with a small sum of money before transferring larger sums. This aids in confirming the accuracy of the data entered as well.
How to Choose a Wallet: Comparison of Popular Options
When you are thinking about creating your own cryptocurrency wallet, it is important to pay attention to successful examples that have already gained the trust of users. The table below summarizes popular wallets.
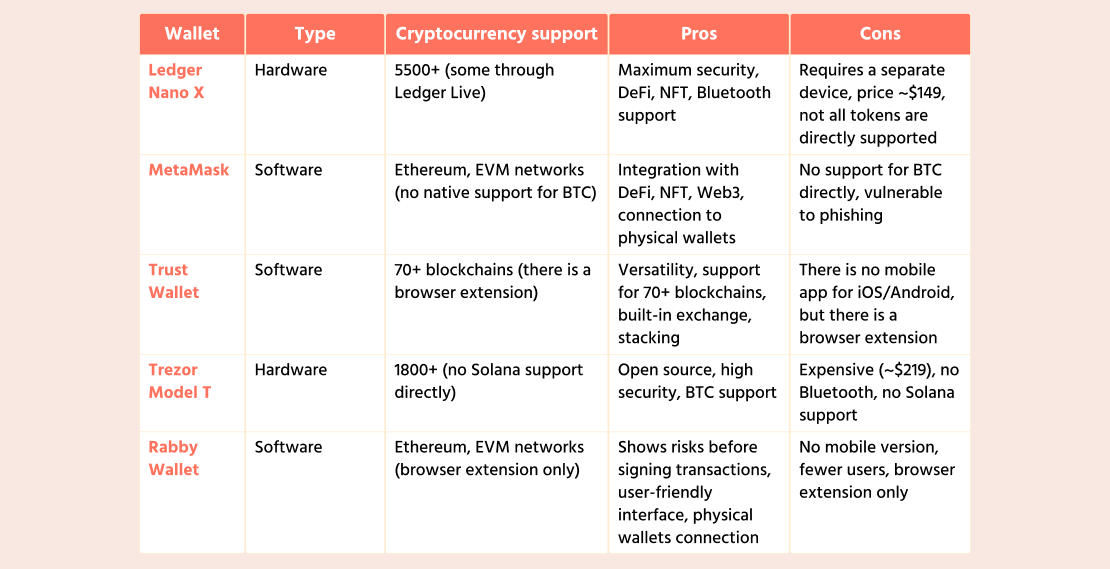
This table provides an overview of global crypto wallets that are popular among users around the world.
How to Develop a Crypto Wallet App
When considering crypto wallet software development, it’s important to understand the features of a crypto wallet that enhance user experience and security. These include support for multiple cryptocurrencies, secure key storage, and integration with blockchain technology.
If you want to create a cryptocurrency wallet, we offer you Crypto Wallet White-label Solution. It is a white-label solution for companies seeking to provide their customers with the best cryptocurrency experience.
The cryptocurrency wallet development process involves several stages, from MVP development to product launch and support. For successful development, it is important to assemble a qualified wallet development company, which may include blockchain wallet developers, frontend and backend specialists, testers, and project managers.
When designing wallets, it is also important to consider the types of wallets that will be supported. For example, mobile wallets are convenient for users who want to manage assets from their phones, while paper wallets provide offline storage of keys in physical form.
Various methods such as data encryption, two-factor authentication (2FA), and integration with hardware modules are used to secure your wallet. In addition, it is important to consider legal aspects such as KYC (Know Your Customer) and AML (Anti-Money Laundering) compliance, as well as the protection of users’ personal data in accordance with GDPR.
Crypto Wallet App Development Cost
The development cost of a crypto wallet depends on many factors, such as the complexity of the functionality, the choice of platform (mobile cryptocurrency app, web wallet, or hardware solution), the size of the app, and the level of security. For example, integration with hardware crypto wallets or multi-signature support may increase the overall cost but will significantly enhance security.
When you decide to create a crypto wallet app, partnering with a reliable app development company can help streamline the process and ensure that your wallet app must meet all security and usability standards. The cost to develop a crypto wallet starts at 20,000 and can go up to 100,000, depending on the functionality. Adding complex features such as staking can further increase the overall cost of development by 20–30%. However, the cost of developing a wallet can be reduced by using open-source solutions such as MyEtherWallet.
To ensure that the wallet is user-friendly, consider integrating features like wallet using the QR code for easy transactions. Additionally, launching your Bitcoin wallet app on the app store can help reach a wider audience and contribute to the success of your crypto wallet.
If you are developing a cryptocurrency wallet app or developing a Bitcoin wallet, it’s crucial to account for development cost and the factors that influence it. For instance, an app with a basic feature set may cost you around $20,000, while more advanced features can significantly increase the overall cost.
Conclusion
While some governments are indecisive about whether to legalize cryptocurrencies in their countries and others even ban them, crypto trading is gaining popularity at a breakneck speed. In the near future, digital currency trading will become an integral part of the global economy, yet many governments are already considering how to adjust their legislation to adopt it.
Currently, many startups are experimenting with blockchain and actively investing in the crypto wallet development process, searching for the most skilled developers for that. SCAND has extensive experience in working with blockchain app development solutions. Take the lead in the crypto market and create a crypto wallet with a development team of professionals from SCAND.












